Wait queues
Wait queues have several uses in the kernel, particularly for interrupt handling, process synchronization, and timing. Because these topics are discussed in later chapters, we'll just say here that a process must often wait for some event to occur, such as for a disk operation to terminate, a system resource to be released, or a fixed interval of time to elapse. Wait queues implement conditional waits on events a process wishing to wait for a specific event places itself in the proper wait...
The Ext3 Journaling Filesystem
The idea behind Ext3 journaling is to perform any high-level change to the filesystem in two steps. First, a copy of the blocks to be written is stored in the journal then, when the I O data transfer to the journal is completed (in short, data is committed to the journal), the blocks are written in the filesystem. When the I O data transfer to the filesystem terminates (data is committed to the filesystem), the copies of the blocks in the journal are discarded. While recovering after a system...
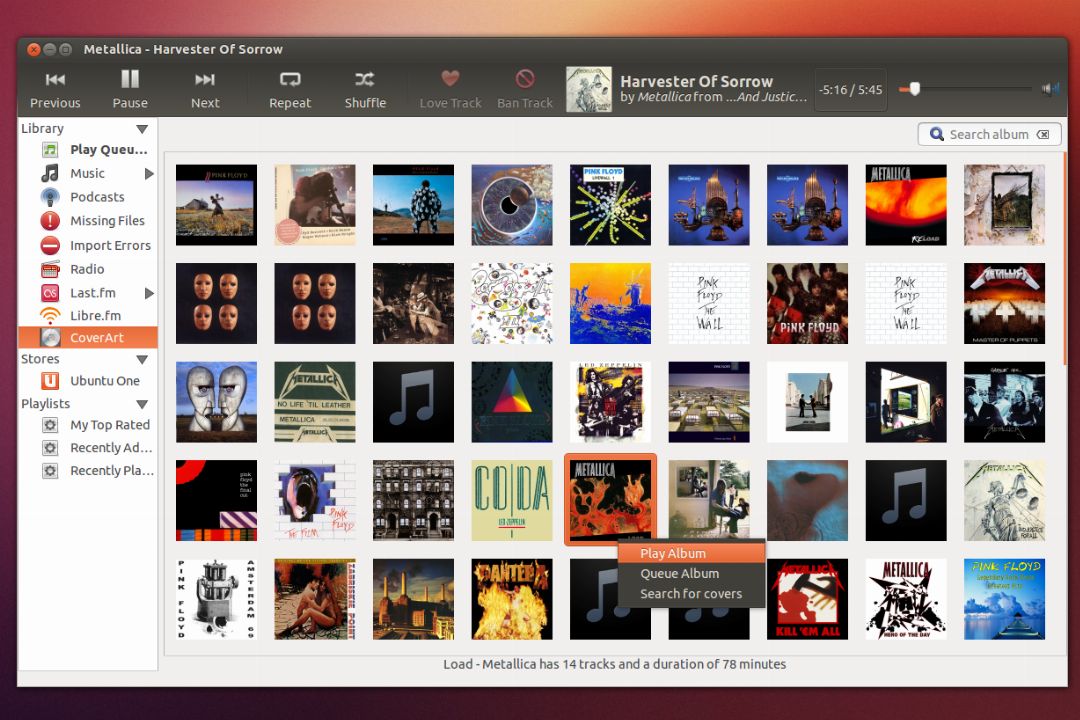
Producing and viewing mailserver statistics with isoqlog
If you wish to keep track of the mail sent and received by a machine then isoqlog is a nice solution allowing you to view your top mail senders and receivers. It works with exim , postfix , sendmail , and qmail . Whilst it doesn't provide a full monitoring solution in the same way that munin, or cacti would it does allow you to keep track of mailserver performance and throughput in a readable fashion.
Files on u01
Underneath the first mount point, create an app subdirectory. This is where the application runs. Next, on u01 app, create an oracle subdirectory. Beneath the u01 app oracle directory, an important split takes place. The subdirectories product, local, and admin are created, as shown Under product, each version of the Oracle database is installed. For example, if you were running Oracle 7.3.4 and Oracle 8.1.6 on the same machine, you would have u01 app oracle product 7.3.4 11 8.1.6 This is an...
Atomic Operations
Several assembly language instructions are of type read-modify-write that is, they access a memory location twice, the first time to read the old value and the second time to write a new value. Suppose that two kernel control paths running on two CPUs try to read-modify-write the same memory location at the same time by executing nonatomic operations. At first, both CPUs try to read the same location, but the memory arbiter (a hardware circuit that serializes accesses to the RAM chips) steps in...
How To : Install/Upgrade to Linux Kernel 3.10.30 LTS in Ubuntu/Linux Mint Systems
The Linux Kernel 3.10.30 LTS is now available for the users and users should upgrade , announced Greg Kroah-Hartman.This Linux Kernel version comes with plenty of changes with respect to drivers, including i915, nouveau, radeon, and mcc (Refer to this article for more details). This article will guide you to install or upgrade to Linux Kernel 3.10.30 LTS in your Ubuntu or Linux Mint system. InstallationFor 32-Bit Systems Download the .deb packages. wget wget wget Install them.
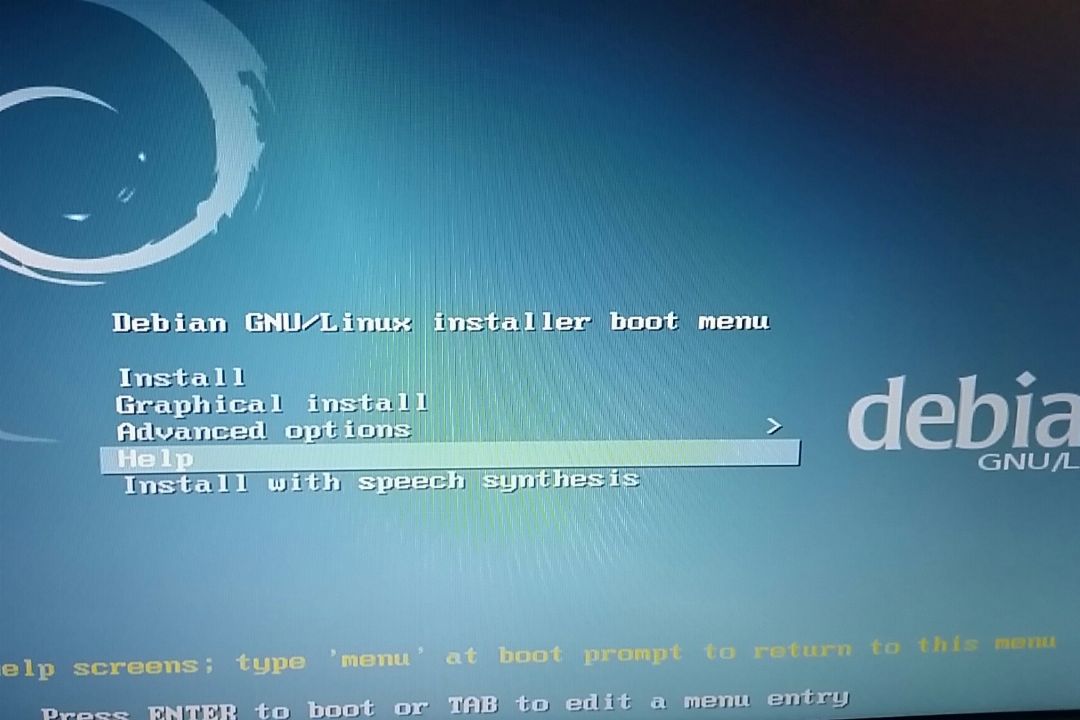
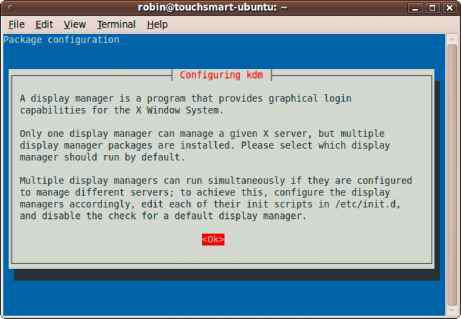
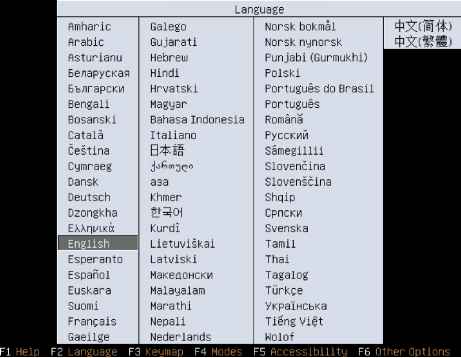
Choosing and Installing a Linux Distribution
Chapter 7 Installing Linux 253 Choosing a Linux Linux at Work Other Distributions Getting Your Own Linux Distribution Finding Another Linux Understanding What You Need Downloading the Distribution Burning the Distribution to CD Exploring Common Installation Knowing Your Computer Hardware Upgrading or Installing from Scratch Dual Booting with Windows or Just Linux Using Installation Boot Options Partitioning Hard Partitioning with Disk Druid During Installation Partitioning with fdisk Tips for...
Writing Sequential File Handlers
Basically, an instance of struct file_operations that provides pointers to some seq_ routines must be implemented to benefit from the sequential file standard implementation. The kprobes subsystem does this as follows static struct file_operations debugfs_kprobes_operations .open kprobes_open, This instance of file_operations can be associated with a file by the methods discussed in Chapter 8. In the case of kprobes, the file will be created in the debugging filesystem see Section 10.2.3. The...
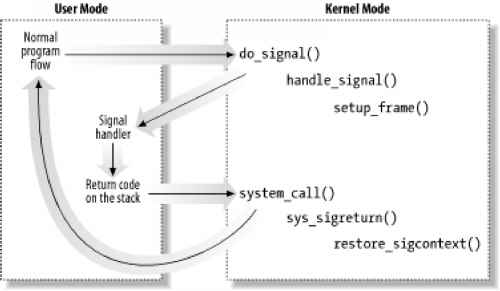
Catching the Signal
If a handler has been established for the signal, the do_signal( ) function must enforce its execution. It does this by invoking handle_signal( ) handle signal(signr, ka, & info, oldset, regs) return 1 Notice how do_signal( ) returns after having handled a single signal. Other pending signals won't be considered until the next invocation of do_signal( ). This approach ensures that real-time signals will be dealt with in the proper order. Executing a signal handler is a rather complex task...
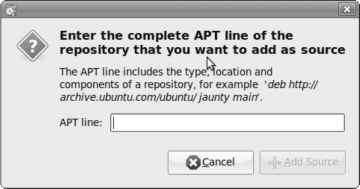
Resolving problems with APT
APT itself takes great care not to leave behind broken dependencies. However, an administrator can put the APT database into an inconsistent state by using dpkg parallel to APT. While APT should make direct use of dpkg obsolete, it is still needed 28Another possibility is the removal of a package from the archive. In such case, it would be a loss to erase the DEB file until an alternative to the software it provides has been found. http snapshot.debian.net can help in such a situation as it...
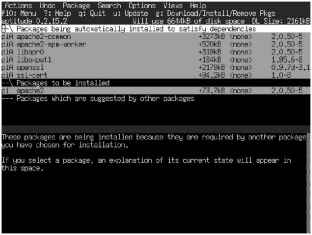
Synaptic Package Manager
The Synaptic Package Manager gives you more control over all your packages. Packages are listed by name and include supporting packages such as libraries and system-critical packages. You can start up Synaptic by choosing System Administration Synaptic Package Manager. Buttons at the lower left of the Synaptic Package Manager window provide options for organizing and refining the list of packages shown (see Figure 6-5) Sections, Status, Origin, Custom Filters, and Search Results. The dialog...
Post Script Printer Definitions PPD Files
The PostScript Printer Definition (PPD) language was developed for graphics, and adapted for the first Apple LaserWriter printers. Many developers give this hardware software combination credit for starting the desktop publishing revolution in the 1980s. Without getting into the details of PPD, such drivers are available for many printers, and can be installed on Linux and Microsoft Windows operating systems. There are a variety of packages of PPD print drivers available. The following command...
Security Mailing Lists and Newsgroups
One of the problems with security Web sites is that they require constant mooitoriog. Fortunately, there are other types 1f resources that are more active in getting information to you. In particular, mailing lists are a means of communication that allow mail from individuals to reach an entire group of readers as quickly as the e-mail system can cperate. Many security mailing lists don't allow posting from members they exist solely to distribute information from the list maintainer. If you...
The SUSE Rescue System
We have talked about fixing system problems by changing the boot runlevel of the system temporarily, but what if you encounter a dire problem such as forgetting the root password This requires another approach because you will need the root password at some point. dev fdG on media floppy type subfs Loading required kernel nodules done Restore device permissions done Activating remaining swap-devices in etc fstab done Sett i ng schedu1i ng t imes1 ices unused Setting up hostname 'bible' done...
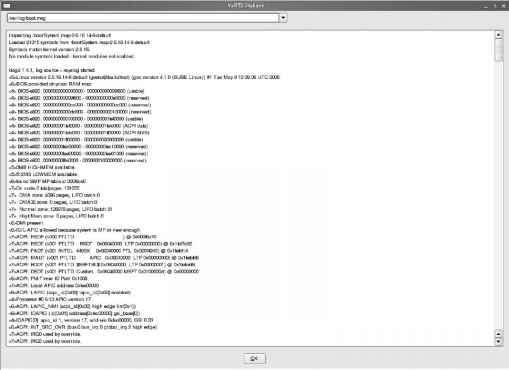
Reading the Boot Messages
When SUSE Linux Enterprise Server starts, you'll see a lot of messages scrolling by on the screen of your server. These messages are generated by the kernel and indicate whether everything is going well. Unfortunately, the messages scroll by way too fast for you to be able to read what's happening. Fortunately, you have two ways to monitor what has happened when your system has finished booting. The first method to get more information about the boot procedure is to use the dmesg command on the...
Professional Linux Kernel Architecture
10475 Crosspoint Boulevard Indianapolis, IN 46256 www.wiley.com Copyright 2008 by Wolfgang Mauerer Published by Wiley Publishing, Inc., Indianapolis, Indiana Manufactured in the United States of America 10 987654321 Library of Congress Cataloging-in-Publication Data Professional Linux kernel architecture Wolfgang Mauerer. p. cm. Includes index. ISBN 978-0-470-34343-2 (pbk.) 1. Linux. 2. Computer architecture. 3. Application software. I. Title. QA76.9.A73M38 2008 005.4'32--dc22 No part of this...
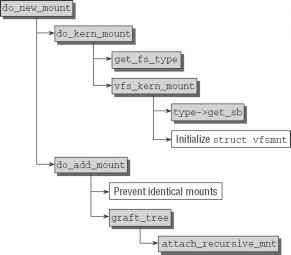
The Mount System Call
The point of entry for the mount system call is the sys_mount function defined in fs namespace.c. Figure 8-5 shows the associated code flow diagram. Figure 8-5 Code flow diagram for sys_mount. Figure 8-5 Code flow diagram for sys_mount. The approach described here is used only to mount a new filesystem in an existing root filesystem. A modified version of the above algorithm mounts the root filesystem itself, but is not sufficiently interesting to merit a separate description (its code can be...
An introduction to bash completion: part
One of the nicest facilities of the modern shell is the built in completion support. These facilities allow you to complete commands and their arguments easily. Read on for a brief introduction to adding your own command completions. Most shells allow command completion, typically bound to the TAB key, which allow you to complete the names of commands stored upon your PATH, file names, or directory names.
The Registry vs Text Files
I think of the Windows Registry as the ultimate configuration database thousands upon thousands of entries, very few of which are completely documented, some located on servers and some located on clients. While it is possible to edit Registry entries manually, the fact that one does so using a graphical tool doesn't make the process intuitive. Consider this Windows .NET Server Registry setting In HKEY_LOCAL_MACHINE Management PrefetchParameters, set EnablePrefetcher to 0x00000003 to enable...
Tutorial Virtual Hosting Email with Sendmail
Virtual hosting is a rather broad term applied to many network services to specify that the server in question provides service to two or more network domains with some degree of separation. Specifically, in the case of a mail server, it means that the mail server will deliver to a unique local user based on the user name and the domain in the to field of the received email. For example, an email to joe swelltech.com would be treated differently from an email sent to joe notswelltech.com and...
Creating an AIDE Configuration File
After AIDE has been installed, the first thing you'll want to do is create a configuration file. Unlike most other software in Linux, AIDE doesn't include a default configuration file from which you can build a customized version. There is a sample configuration file in the < AiDE-source> doc directory, but it explicitly states that you shouldn't use it as a system-wide configuration file. Therefore, you'll have to build one of your own. Don't worry, I'm here to help. The AIDE configuration...
Seven Easy Steps To Setting Up An Interal DNS Server On Ubuntu
Bind9 is used all across the internet for DNS. A survey shows that over 70 of DNS servers on the internet use Bind. In this tutorial we will setup a Bind9 DNS server for your home network with caching. By running a caching DNS server it will cache DNS locally so sites you visit often will not have to make a DNS query until the DNS record has expired. This will help improve your internet speed as well as reduce bandwidth.
Understanding and improving Nextcloud Previews
NextCloudPi s target audience is domestic hosters and one of the use cases that attracts users is to self-host their own picture collection. The main complaint for such users is that gallery is too slow. When you open the gallery previews are generated on the fly which affects responsiveness. Once they are generated, the next time it will load much faster.
Process Monitor Process PMON
Process Monitor (PMON) cleans up abnormally terminated user processes. This includes rolling back a process's transaction and releasing its resources such as transaction locks and memory. PMON also detects and resolves deadlocks by rolling back the deadlocking transaction. If the database is set to use MTS, PMON will restart dispatcher and server processes that have died unnaturally. PMON can take a while to wake-up because killed user processes can exist for quite some time. I have seen user...
Configuring Clients for NIS
This section explains how to set up a NIS client for the server started in the previous section. As with setting up a NIS server, NIS clients can be configured using command-line utilities or by taking advantage of YaST's graphical administrative interface. The following two sections explain how to configure a NIS client using each of these methods. YaST makes NIS client configuration almost trivial, using a single dialog box to collect information about the NIS domain that you want your client...
Understanding the Fatal Signal 11 Error
Some people get a fatal signal 11 error during installation. This usually happens past the initial boot screen as the anaconda installer is starting its GUI or text interface. The most likely cause of a signal 11 error during installation is a hardware error related to memory or the cache associated with the CPU (microprocessor). Signal 11, also known as SIGSEGV (short for Segment Violation Signal), can occur in other Linux applications. A segment violation occurs when a process tries to access...
Genkernel menuconfig all
After you have made any changes you want to your kernel configuration, select Exit, and then choose Yes to save it. At this point, genkernel makes your new kernel. This takes a while. After genkernel is complete, note the names of the kernel and boot loader. (Type ls boot to see the names.) 25. Add coldplug. Type the following to enable coldplug (so hardware outside of that which is detected during initialization is detected and configured automatically) 26. Configure system services. Install...
Replacing Hard Coded Passwords with Variables
Traditionally when a password is required in shell script it has been hard-coded into the script. Using this hard-coded technique presents us with a lot of challenges, ranging from a security nightmare to the inability to change key passwords on a regular basis. The variable technique presented in this section is very easy to implement with only minor changes to each shell script. NOTE Important Each shell script must be changed in order to properly implement the technique throughout the...
Managing Hardware Devices
Use the YaST Control Center's Hardware category to access GUI tools that enable you to control various devices. Figure 17-5 shows the different types of devices you can manage from YaST Control CenterOHardware. Figure 17-5 Manage hardware devices through YaST Control Center's Hardware category. Figure 17-5 Manage hardware devices through YaST Control Center's Hardware category.
Reader Writer Locks
The mechanisms described above have one disadvantage. They do not differentiate between situations in which data structures are simply read and those in which they are actively manipulated. Usually, any number of processes are granted concurrent read access to data structures, whereas write access must be restricted exclusively to a single task. The kernel therefore provides additional semaphore and spinlock versions to cater for the above these are known accordingly as Reader Writer semaphores...
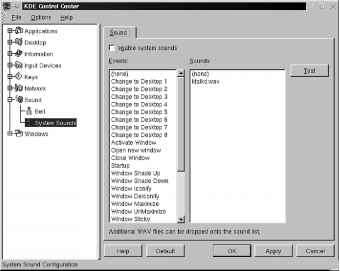
Defining Sound Events
KDE also lets you define a specific sound for each of over two dozen events. To view the Sound dialog box, choose the System Sounds item in the Sound section of the Control Center (see Figure 7.21). The Events list shows you which things you can assign a sound to. For example, if you assign a sound to the Logout event, that sound will play each time you choose Logout from the main menu (or another location). All the sound files must be located in opt kde share sounds, and all sound files must...
Busy Box init
Among the commands it supports by default, BusyBox provides init-like capabilities. As with the original mainstream init, BusyBox can handle the system's startup. BusyBox init is particularly well adapted to embedded systems, because it provides most of the init functionality an embedded system typically needs without dragging the weight of the extra features found in System V init. Also, because BusyBox is a single package, there is no need to keep track of an additional software package when...
How sendmail Works
Outbound email When you send email, the MUA passes the email to sendmail, which creates in the var spool mqueue mail queue directory two files that hold the message while sendmail processes it. To create a unique filename for a particular piece of email, sendmail generates a random string and uses that string in filenames pertaining to the email. The sendmail daemon stores the body of the message in a file named df data file followed by the generated string. It stores the headers and other...
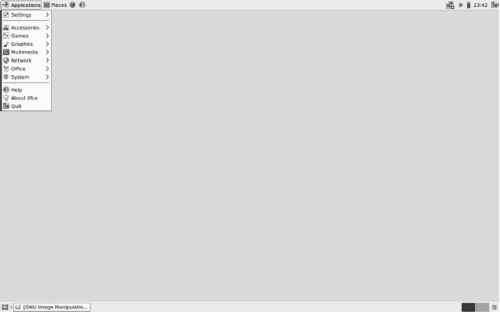
Ubuntu Administrative Tools
Administration is handled by a set of separate specialized administrative tools developed and supported by Ubuntu, such as those for user management and display configuration. To access the GUI-based Ubuntu tools, you log in as a user who has administrative access. (This is the user you created when you first installed Ubuntu.) On the GNOME desktop, you can access system administrative tools from the System Administration menu. Here you will find tools to set the time and date, to manage users,...
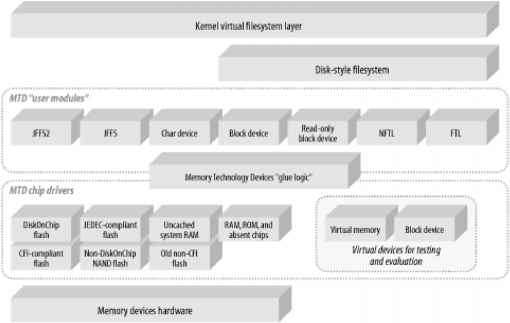
Memory Technology Devices
In Linux terminology, memory technology devices (MTDs) include all memory devices, such as conventional ROM, RAM, flash, and M-Systems' DiskOnChip (DOC). As explained by Michael Barr in Programming Embedded Systems in C and C++ (O'Reilly), such devices have their own capabilities, particularities, and limitations. Hence, to program and use an MTD device in their systems, embedded system developers traditionally use tools and methods specific to that type of device. To avoid, as much as...
FedoraRHEL Configuration Tools
Most of the Fedora RHEL configuration tools are named system-config-*. These tools bring up a graphical display when called from a GUI some display a textual interface when called from a non-GUI command line. Some, such as system-config-firewall-tui, use a name with a -tui extension for the textual interface. In general, these tools, which are listed in Table 11-2, are simple to use and require little explanation beyond what the tool presents. Some have Help selections on their toolbar most do...
Fedora Administration Tools
On Fedora, most administration tasks can be handled by a set of separate specialized administrative tools developed and supported by Red Hat Linux and Fedora, such as those for user management and display configuration. Many of these are GUI-based and will work on any X Window System environment, such as GNOME or KDE. To access the GUI-based Red Hat and Fedora tools, you log in as the root user to the GNOME desktop and select the System menu. System administrative tools are listed on the...
Using graphical administration tools
The trend over the past few versions of Fedora and Red Hat Enterprise Linux has been to steer clear of the massive administrative interfaces (such as linuxconf and Webmin) and instead to offer graphical windows that perform individual administrative tasks. Instead of sharing one monolithic interface, they share common menus. Individual graphical windows for configuring a network, adding users, or setting up printers can be launched from those menus. There may be times when your desktop (and...
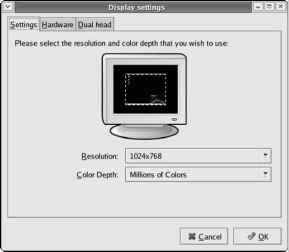
Configuring XOrg X11 Using systemconfigdisplay
Fedora Core includes a GUI utility called system-config-display, written in the Python programming language, that enables you to configure X. The system-config-display utility provides a convenient way to configure X through a GUI that itself uses X. To run it, type system-config-display at a shell prompt or, if you are already on the GNOME desktop, select Desktop O System Settings O Display from GNOME's top panel. The utility probes the monitor and video card. Then it starts X (if X is not...
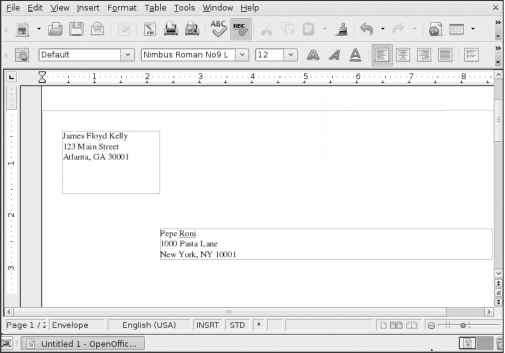
Printing Envelopes
One nice feature that Writer supports is the ability to print envelopes if your printer supports this function. To print an envelope, first load your printer with a blank envelope consult your printer's documentation for proper orientation and insertion of an envelope. Next, open a new Writer document, click the Insert menu, and choose the Envelope option. A window opens, in which you can type your address in the Sender box and the recipient's address in the Addressee box (see Figure 5-16).
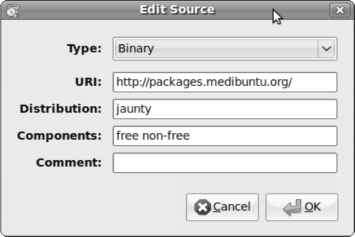
Managing Software Repositories
The knowledge of which software you can install comes from software repositories because they let the computer know which software is available. You saw a repository in Chapter 6, in the section Installing Media Support Using the Medibuntu Repositories. Software repositories are a key component in working with Ubuntu, and they're the reason why software management works completely different in Ubuntu as compared to in Windows or on a Mac. In Windows or on a Mac, if you want to install software,...
The Development Environment
The development process for a mobile device tends to be different from the normal process that you might use when you develop on a workstation or server. Often you'll need to generate a complete OS image from scratch in a working environment, which you'll then install on the target device. In the case of the Ubuntu Mobile project, a complete set of built packages is available to the developer, so many of the complexities that are typically associated with existing build- your- own...
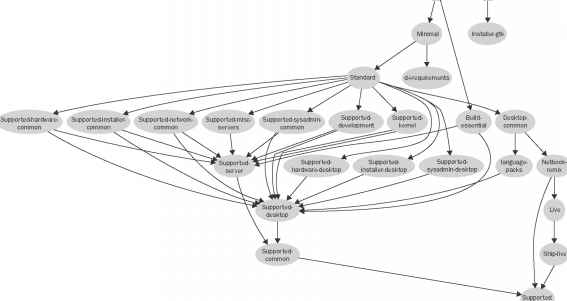
Installation
You have a few options when it comes to installing Ubuntu distributions, as described in Chapter 2, ranging from installing one as your main operating system to adding it alongside another operating system or even within a virtual machine. But whichever method you choose, you'll need the original ISO file. For your convenience, the most popular Ubuntu derivative ISO files are included in the distros folder of the DVD supplied with this book, and their filenames are listed in Table 15-1. Table...
Preparing for the Ubuntu Netbook Remix Installation
On most netbooks, Windows is preinstalled. The first thing to do is replace that with Ubuntu Netbook Remix. Before you begin to install Ubuntu Netbook Remix, check that your netbook meets the following minimum requirements suggested by the developers 4 GB flash disk or hard disk For a more detailed list of compatible hardware, check which groups hardware into tiers of compatibility. To install Ubuntu Netbook Remix, you need two things to start with. Because a netbook doesn't have an optical...
Installing and Upgrading Ubuntu
In this chapter, we'll take a look at the companion DVD for this book, which is attached to the inside back cover, and I'll also show readers without access to the DVD how to get the same software by downloading and burning ISO disc images. Unlike most program discs you may have used, this DVD is unusual in that you don't actually have to install anything if you don't wish to, because it's been set up as a Live This means that the DVD itself is a fully working installation of Ubuntu 9.10 that...
Putting It All Together
This chapter walks you through the process of creating a custom distribution of Ubuntu Mobile, which could potentially be used by an OEM to go to market. It could just as easily be used by a homebrewer who wishes to resurrect an old, unused mobile device that's gathering dust. Like beer making, no special equipment (apart from a laptop and Internet connection) is needed to create your image. Choosing a good beer recipe and following good brewing procedures can give you top quality beer even...
Ubuntu Netbook Edition
This edition of Ubuntu (known as Netbook Remix in versions of Ubuntu prior to 10.04) is a different kettle of fish altogether, because it's been totally redesigned specifically for use on Netbook PCs (see Figure 15-9), which generally have less processing power and smaller screens. If you have such a device and find your current operating system to be slow and somewhat unresponsive, the Netbook Edition may be just what you need. Ixxl 41 jsC g Thu Nov 26, 8 30 AM ( ) robin Figure 15-9. The...
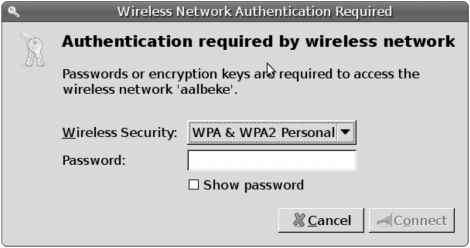
Managing the Keyring
Probably the most misunderstood component in Ubuntu is the Keyring application. The purpose of the keyring is to manage your passwords and keys. Many applications require the use of a password or some other form of authentication. As a result, the user has to remember too many passwords, and they risk losing access because they can't remember the right password. The keyring offers a solution for this problem. The idea is simple the keyring stores all your passwords and encryption keys. When you...
Installing Media Support Using the Medibuntu Repositories
Before you begin to work with the Medibuntu repositories, you should know what sort of software they contain. They provide two types of software packages. The first kind are free as in freedom (open source) but legally problematic in some countries. This is the reason you won't ever find this software in the official Ubuntu repositories. You can install and use these packages, but doing so is completely at your own risk. (You shouldn't be worried when using the software described in this...
Configuring NFS Kernel Server Options
Options for the common NFS services for an NFS server are set in the file etc default nfs-kernel-server, which you can edit using your favorite text editor. Each of the following options is defined in a setting that looks like setting value, where value is one of yes or no. The options that you should set are the following RPCNFSDCOUNT Set this to a specific numeric value to identify the number of NFS daemon instances that you want to start. The default value, 8, is usually sufficient, although...
The Linux Desktop Environment
In the early days of Linux (the early 1990s), all that was available was a simple text interface to the Linux operating system. This text interface allowed administrators to start programs, control program operations, and move files around on the system. With the popularity of Microsoft Windows, computer users expected more than the old text interface to work with. This expectation spurred more development in the OSS community, and the advent of Linux graphical desktops emerged. Linux is famous...
Superb Software List
This package resource list has the best Karmic-compliant software, by category, for work or play. Fonts, multimedia codecs, system tools, you name it. With our repositories nicely set up, we're set to install some nice software. This works pretty much as before, with Jaunty. The only change I've found is that, for those packages not from repositories but downloaded from the software providers themselves, instead of these downloading to home USERNAME Desktop, they download to home USERNAME...
The Gnome Desktop
GNOME (pronounced guh-nome) provides the desktop environment that you get by default when you install Fedora, Ubuntu, and other Linux systems. This desktop environment provides the software that is between your X Window System framework and the look-and-feel provided by the window manager. GNOME is a stable and reliable desktop environment, with a few cool features. As of this writing, GNOME 2.26 is the most recent version available, although the distribution you are using may or may not...
Routing Data Structures
The most important function of the IP layer consists of ensuring that packets originated by the host or received by the network interface cards are forwarded toward their final destinations. As you might easily guess, this task is really crucial because the routing algorithm should be fast enough to keep up with the highest network loads. The IP routing mechanism is fairly simple. Each 32-bit integer representing an IP address encodes both a network address, which specifies the network the host...
Routing and the IPv6 FIB
The Linux IPv6 routing implementation is similar to IPv4 and shares some of the Linux networking framework. Like IPv4, route tables are used for both input and output packets because this is a flexible way of determining both machine local and external destinations in a transparent way. Like, IPv4, IPv6 contains a routing cache based on the generic destination cache. Unfortunately, though, it does not yet use the same Forwarding Information Base (FIB) as IPv4. Instead, IPv6 has its own FIB.
Exam 101 Practice Test
Exam 101 consists approximately of 60 questions. Most are multiple-choice singleanswer, a few are multiple-choice multiple-answer, and the remainder are fill-in questions. No notes or other materials are permitted, and you have 90 minutes to complete the exam. The answers are provided on page 224. 1. What section of the online user's manual and command reference holds administrative (not user) commands Select one. 2. What two commands will display the status of processes on a Linux system...
Obtaining and Installing TCPDump
TCPDump can be downloaded from http www.tcpdump.org . TCPDump requires the PCap library libpcap, so while you're downloading TCPDump, you should download libpcap as well. Most popular Linux distributions such as SUSE also include TCPDump as an available package. For example, if you're using Debian you can simply type this The package maintenance system will install TCPDump and any prerequisites too. For everyone else, you can probably search your distribution's repository for a package or just...
Reexecution of System Calls
The request associated with a system call cannot always be immediately satisfied by the kernel when this happens, the process that issued the system call is put in a TASK_INTERRUPTIBLE or TASK_UNINTERRUPTIBLE state. If the process is put in a task_interruptible state and some other process sends a signal to it, the kernel puts it in the task_running state without completing the system call (see Section 4.8). When this happens, the system call service routine does not complete its job, but...
Writing Dirty Buffers to Disk
Unix systems allow the deferred writes of dirty buffers into block devices, since this noticeably improves system performance. Several write operations on a buffer could be satisfied by just one slow physical update of the corresponding disk block. Moreover, write operations are less critical than read operations, since a process is usually not suspended because of delayed writings, while it is most often suspended because of delayed reads. Thanks to deferred writes, each physical block device...
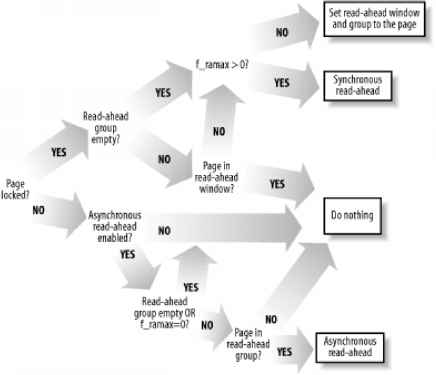
Reading and Writing a File
Section 12.6.2, described how the read( ) and write( ) system calls are implemented. The corresponding service routines end up invoking the file object's read and write methods, which may be filesystem-dependent. For disk-based filesystems, these methods locate the physical blocks that contain the data being accessed, and activate the block device driver to start the data transfer. Reading a file is page-based the kernel always transfers whole pages of data at once. If a process issues a read(...
The getblk Function
The getblk( ) function is the main service routine for the buffer cache. When the kernel needs to read or write the contents of a block of a physical device, it must check whether the buffer head for the required buffer is already included in the buffer cache. If the buffer is not there, the kernel must create a new entry in the cache. To do this, the kernel invokes getblk( ), specifying as parameters the device identifier, the block number, and the block size. This function returns the address...
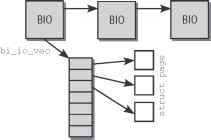
Generic Hard Disks and Partitions
While struct block_device represents a block device toward the device driver level, another abstraction emphasizes the connection with generic kernel data structures. From this point of view, the block devices by themselves are not interesting. Instead, the notion of a hard disk, possibly with subpartitions, is more useful. The partition information on a device is independent of the block_device instances that represent the partitions. Indeed, when a disk is added to the system, the kernel...
Request Queues
Read and write requests to block devices are placed on a queue known as a request queue. The gendisk structure includes a pointer to the device-specific queue, which is represented by the following data type. Together with queue_head for cacheline sharing struct request_list rq Queue request freelists prep_rq_fn prep_rq_fn unplug_fn unplug_fn merge_bvec_fn merge_bvec_fn prepare_flush_fn prepare_flush_fn softirq_done_fn softirq_done_fn unplug_timer unplug_thresh unplug_delay unplug_work After...
Request Structure
The kernel provides its own data structure to describe a request to a block device. sector_t sector * next sector to submit * sector_t hard_sector * next sector to complete * unsigned long nr_sectors * no. of sectors left to submit * unsigned long hard_nr_sectors * no. of sectors left to complete * * no. of sectors left to submit in the current segment * unsigned int current_nr_sectors * no. of sectors left to complete in the current segment * unsigned int hard_cur_sectors struct bio *bio...
Delivering a Signal
We assume that the kernel noticed the arrival of a signal and invoked one of the functions mentioned in the previous section to prepare the process descriptor of the process that is supposed to receive the signal. But in case that process was not running on the CPU at that moment, the kernel deferred the task of delivering the signal. We now turn to the activities that the kernel performs to ensure that pending signals of a process are handled. As mentioned in Section 4.8, the kernel checks the...
Dequeue a signal
The function shown in Figure 18.30, from kernel signal .c, takes a signal off the queue and returns the information about it to the caller, which is expected to be holding the sigmask_lock. siginfo_t*info) 244 sig next_signal(current, mask) sig)) 248 if 249 current-> sigpending 0 2 50 return 0 printk( d-> d n, signal_pending(current), sig) the parameters are a pointer to the blocked mask of the current process and a struct siginfo into which the extra information about the signal being...
Handling a Faulty Address Outside the Address Space
If address does not belong to the process address space, do_page_fault( ) proceeds to execute the statements at the label bad_area. If the error occurred in User Mode, it sends a sigsegv signal to current (see Section 10.2) and terminates up read(& tsk-> mm-> mmap sem) if (error code & 4) * User Mode * tsk-> thread.cr2 address tsk-> thread.error code error code tsk-> thread.trap no 14 info.si_signo SIGSEGV info.si errno 0 info.si addr (void *) address force_sig_info(SIGSEGV,...
Posix Apis and System Calls
Let's start by stressing the difference between an application programmer interface (API) and a system call. The former is a function definition that specifies how to obtain a given service, while the latter is an explicit request to the kernel made via a software interrupt. Unix systems include several libraries of functions that provide APIs to programmers. Some of the APIs defined by the libc standard C library refer to wrapper routines (routines whose only purpose is to issue a system...
Understanding the Linux Kernel 2nd Edition
The Audience for This Book Organization of the Material Overview of the Book Background Information Conventions in This Book How to Contact Us Acknowledgments Section 1.1. Linux Versus Other Unix-Like Kernels Section 1.2. Hardware Dependency Section 1.4. Basic Operating System Concepts Section 1.5. An Overview of the Unix Filesystem Section 1.6. An Overview of Unix Kernels Section 2.1. Memory Addresses Section 2.2. Segmentation in Hardware Section 2.3. Segmentation in Linux Section 2.4. Paging...
System Call Handler and Service Routines
When a User Mode process invokes a system call, the CPU switches to Kernel Mode and starts the execution of a kernel function. In Linux a system call must be invoked by executing the int 0x8 0 assembly language instruction, which raises the programmed exception that has vector 128 (see Section 4.4.1 and Section 4.2.4, both in Chapter 4). Since the kernel implements many different system calls, the process must pass a parameter called the system call number to identify the required system call...
Implementing Timer Handling
Handling of all timers is initiated in update_process_times by invoking the run_local_timers function. This limits itself to using raise_softirq TIMER_SOFTIRQ to activate the timer management softIRQ, which is executed at the next opportunity.8 run_timer_softirq is used as the handler function of the softIRQ it selects the CPU-specific instance of struct tvec_t_base_s and invokes_run_timers. _run_timers implements the algorithm described above. However, nowhere in the data structures shown is...
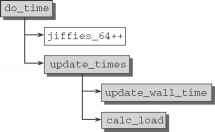
Timer Activation and Process Accounting
As the time base for timers, the kernel uses the timer interrupt of the processor or any other suitable periodic source. On IA-32 and AMD64 systems, the programmable interrupt timer (PIT) or the High Precision Event Timer (HPET) can be employed for this purpose. Nearly all modestly modern systems of this type are equipped with an HPET, and if one is available, it is preferred to the PIT.3 The interrupt occurs at regular intervals exactly HZ times per second. HZ is defined by an...
The timer interrupt handler
The function shown in Figure 15.2, from kernel timer.c, is the root of all timer interrupt handling. It is called on every timer interrupt. It is short and to the point. 674 void do_timer(struct pt_regs * regs) 675 676 (* (unsigned long * )&jiffies;)++ 677 ifndefCONFIG_SMP 681 endif 682 mark_bh(TIMER_BH) 683 if(TQ_ACTIVE(tq_timer)) 684 mark_bh(TQUEUE_BH) 685 Figure 15.
Creating and Registering Entries
New entries are added to the proc filesystem in two steps. First, a new instance of proc_dir_entry is created together with all information needed to describe the entry. This instance is then registered in the data structures of proc so that it is visible to the outside. Because the two steps are never carried out independently of each other, the kernel makes auxiliary functions available to combine both actions so that new entries can be generated quickly and easily. The most frequently used...
Logging with syslog
The traditional Linux logging facility is syslogd. Current versions of SLES and openSUSE offer both syslogd and syslog-ng (ng for new generation''). syslog-ng is now the default in openSUSE and SLES. The basic concepts of logging facilities and log levels apply to both methods syslog-ng (discussed later in the chapter) is essentially an extension of syslogd that has more flexibility and is easier to use as a central log host in a large networked environment. Here we look first at syslogd and...
Allowing ICMP Traffic
It is all well and good having a secure firewall, but you still need to be able to receive ICMP traffic so that your users, you, and other Internet users are aware if there is a problem. Internet Control Message Protocol (ICMP) is integral to the working of the Internet. ICMP is used to send status and error messages about the state of the network to interested parties. For example, when you ping a machine, the ping packet and its echo are sent over ICMP. If you cannot access a machine because...
Final kernel Page Table when RAM size is between 896 MB and 4096 MB
In this case, the RAM cannot be mapped entirely into the kernel linear address space. The best Linux can do during the initialization phase is to map a RAM window having size of 896 MB into the kernel linear address space. If a program needs to address other parts of the existing RAM, some other linear address interval must be mapped to the required RAM. This implies changing the value of some Page Table entries. We'll defer discussing how this kind of dynamic remapping is done in Chapter 7. To...
Final kernel Page Table when RAM size is less than 896 MB
The final mapping provided by the kernel Page Tables must transform linear addresses starting from 0xc000000 0 into physical addresses starting from 0. The _ pa macro is used to convert a linear address starting from PAGE_OFFSET to the corresponding physical address, while the _va macro does the reverse. The kernel master Page Global Directory is still stored in swapper_pg_dir. It is initialized by the paging_init( ) function, which does the following 1. Invokes pagetable_init( ) to set up the...
Figure 102 Code flow diagram for procrootinit
Proc_root_init first creates a slab cache for proc_inode objects using proc_init_inodecache these objects are the backbone of the proc filesystem and often need to be generated and destroyed as quickly as possible. Then the filesystem is officially registered with the kernel using the register_filesystem routine described in Chapter 8. And finally, mount is invoked to mount the filesystem. kern_mount_data is a wrapper function for do_kern_mount, also discussed in Chapter 8. It returns a pointer...
Figure 85 The flow diagram of the Page Fault handler
Dues the deists belongToEhe prate addresi space' The identifiers vmalloc_fault, good_area, bad_area, and no_context are labels appearing in do_page_fault( ) that should help you to relate the blocks of the flow diagram to specific lines of code. The identifiers vmalloc_fault, good_area, bad_area, and no_context are labels appearing in do_page_fault( ) that should help you to relate the blocks of the flow diagram to specific lines of code. The do_ page_fault( ) function accepts the following...
Handling of Page Faults
The association between virtual and physical memory is not established until the data of an area are actually needed. If a process accesses a part of virtual address space not yet associated with a page in memory, the processor automatically raises a page fault that must be handled by the kernel. This is one of the most important and complex aspects of memory management simply because a myriad of details must be taken into account. For example, the kernel must ascertain the following Was the...
The Samba Server
Samba is a full-featured implementation of a Server Message Block (SMB) server, which can offer transparent file services to Windows (95, 98, NT, 2000) clients, as well as to OS 2 clients. The brain child of LinuxCare's Andrew Tridgell back in 1992, Samba is now widely used and updated with help from programmers from all over the world. Samba allows network administrators to use a Linux server's ability to store and manage a large number of files, while still preserving the use of Windows-based...
Configuring Samba
The configuration file provided with the Debian package includes the most common settings. It has been very well commented to help explain many of the settings. The following code is taken from the default install configuration file etc samba smb.conf. The text in bold is discussed following the code. Note that lines starting with semicolons ( ) and pound signs ( ) are ignored when the file is read for configuration settings. This file is included in the chapter to better explain portions of...
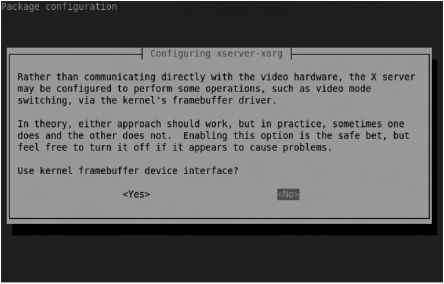
Configure the X Server from the Command Line
Those of you familiar with other Linux distributions may be familiar with the command line configuration tool for the X server. On older distributions, it was known as xf86config on the latest distributions, it's known as xorgconfig. The dpkg-reconfigure xserver-xorg command brings the administrator through a similar series of steps. It's a straightforward process to use the noted command to configure the X server. But before starting this process, back up the current X server configuration...
Installing Debian onto USB flash media with everything encrypted.
This is a simple procedure for installing Debian GNU Linux onto a USB key flash media. It includes several configuration changes but tries to stay as close to a default debian install as possible. This is useful for administrators that need to carry sensitive information or people concerned about their privacy. This was tested on Debian Sid and Knoppix 3.8 with the USB Keys listed below. Tested Media Transcend Jetflash 256MB ( only the base debootstrap install plus a few select packages ).
Using the linux noprobe Command
If the Fedora Core installer does not detect the SCSI controller or network card, you can specify these devices manually by typing linux noprobe at the boot prompt. To see whether the installer deleted the hardware, look for any indication of SCSI or network devices in the messages the Linux kernel displays as it boots. To view these messages during installation, press Ctrl+Alt+F4. The display switches to a text-mode virtual console on which the messages appear. (A virtual console is a screen...
Clone flags
The clone flags determine a whole range of properties of the child process. They are defined in < linux sched.h> , as shown in Figure 8.10. define define define define define define define define define define 0x00000200 0x00000400 0x00000800 0x00001000 0x00002000 0x00004000 0x00008000 0x00010000 define CLONE_SIGNAL (CLONE_SIGHAND CLONE_THREAD) 35 the number of the signal to be sent to the parent process when the child exits is encoded in the low-order 8 bits of the clone flag value. This...
Nonroutable IP addresses
Every machine that is directly connected to the Internet must have a public IP address, commonly known as a routable address. A routable address is one that a connection can be made to from anywhere on the TCP IP network, in this case, the Internet. For example, any web site you visit that is on the Internet has a routable address. If it were non-routable, packets would not be able to be routed to it. Each IP address class has its own non-routable address, which can be used in a private IP...
Monitoring with ARPWatch
ARPWatch is a daemon that watches for new Ethernet interfaces on a network. If a new ARP entry is seen, it could be indicative of a rogue computer somewhere within the network. ARPWatch uses the PCap library, which may not (yet) be on your system. If it's not, you'll find out during the configuration process for ARPWatch. The PCap library, commonly known as libpcap, can be downloaded from http www.tcpdump.org . The PCap library is used for other network and security-related programs such as...
The dentry Cache
Since reading a directory entry from disk and constructing the corresponding dentry object requires considerable time, it makes sense to keep in memory dentry objects that you've finished with but might need later. For instance, people often edit a file and then compile it, or edit and print it, or copy it and then edit the copy. In such cases, the same file needs to be repeatedly accessed. To maximize efficiency in handling dentries, Linux uses a dentry cache, which consists of two kinds of...
Looking at File Internals with the Bless Editor
Very fortunately, there are utilities that can open, display, and enable you to change characters or binary bytes inside any kind of file. These are called binary editors or hexadecimal editors, and the best of them in my experience at least for the Linux world is the Bless Hex Editor. It was designed to operate under graphical user interfaces such as Gnome, and it is very easy to figure out by exploring the menus. Bless is not installed by default under Ubuntu. You can download it free of...
Poll and select
Applications that use nonblocking I O often use the poll and select system calls as well. poll and select have essentially the same functionality both allow a process to determine whether it can read from or write to one or more open files without blocking. They are thus often used in applications that must use multiple input or output streams without blocking on any one of them. The same functionality is offered by two separate functions because they were implemented in Unix almost at the same...
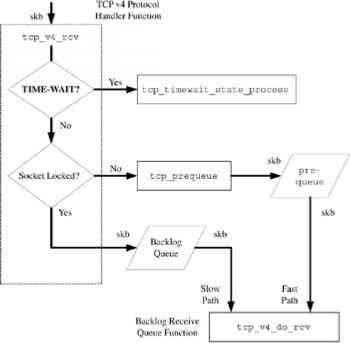
TCP Receive Handler Function tcpv4rcv
In this section, we will examine the TCP input segment handling and the registered handler function for the TCP protocol in the AF_INET protocol family. Figure 10.2 shows the TCP receive packet flow. Figure 10.2 TCP receive packet flow. Figure 10.2 TCP receive packet flow. As is the case with all other member protocols in the AF_INET family, TCP associates a handler function with the protocol field value, IPPPROTO_TCP, (the value six) by initializing an instance of the inet_protocol structure....
Handling IGMP Queries
IGMP queries are sent from routers to the all-hosts. Hosts respond to the queries with membership reports. The function igmp_heard_query processes incoming IGMP queries. static void igmp heard query(struct in device *in dev, struct sk buff *skb, struct igmphdr *ih skb- h.igmph struct igmpv3 query *ih3 (struct igmpv3 query *)ih struct ip mc list *im Group is the multicasting group (class D) address. group ih- group max delay mark 0 The first thing we have to do is figure out if the incoming...
Package Security Check
If you download a software package, you may want to check its integrity and authentication, making sure the package was not tampered with and that it was obtained from a valid source. Yum is configured to automatically perform this check on all software downloaded from your Fedora-compliant repositories. Each repository configuration file in the etd yum.repos.d directory will have its gpgcheck option set to 1.
Civilization Call to Power
You can build online civilizations with Civilization Call to Power (CCP). Like earlier versions and public spin-offs (such as the Freeciv described earlier in this chapter), Civilization Call to Power for Linux lets you explore the world, build cities, and manage your empire. This latest version offers multiplayer network competition and extensions that let you extend cities into outer space and under the sea. CCP is produced by Activision (http www.activision.com ), although the Linux version...