Pointto Point Tunneling Protocol PPTP
The fact that IPsec is a standards-based framework developed under the auspices of the IETF has made it the most widely implemented VPN technology to date. In addition, since IPsec is a mandatory element of a standards-compliant IPv6 implementation, its popularity is only going to increase as the new IP version starts to gain momentum. But there are other competing protocols in the field of virtual private networking that have enjoyed some support from the Linux community. One of those is PPTP.
Developed under the auspices of the Microsoft Corporation, PPTP is an alternative to IPsec that was designed to provide a way to tunnel internal network packets out to remote office users using the Internet. PPTP uses the Point-to-Point Protocol (PPP) as the basis for
tunneling, so all PPTP implementations rely on an existing (or bundled) PPP installation. While PPTP is primarily a packet encapsulation standard, it includes provisions to add connection security in two areas:
Authentication PPTP uses the authentication methods typically supported by PPP devices, both Microsoft and third-party devices such as PAP (Password Authentication Protocol), which is actually not secure at all, and CHAP (Challenge Handshake Authentication Protocol), including its Microsoft and Shiva variants.
Privacy Microsoft defined an optional encryption protocol to be used to protect the privacy of PPTP packet payload as it traverses an untrusted network. The Microsoft Point-to-Point Encryption (MPPE) protocol uses the RC4 encryption algorithm with the password as the seed to generate session keys for encryption.
A PPTP client (typically a Windows laptop or home user) works directly with the PPTP server at the edge of the corporate LAN, as illustrated in Figure 12.9.
Figure 12.9 A look at the protocols used in a PPTP session
Figure 12.9 A look at the protocols used in a PPTP session
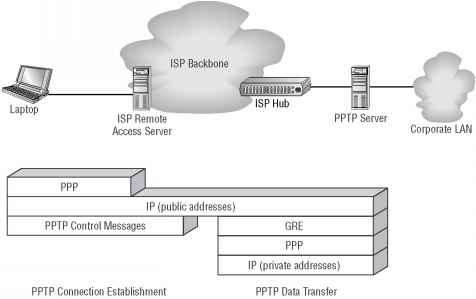
Once the PPTP client has established IP connectivity, typically over PPP to the ISP's nearest remote access server (RAS), it uses PPTP messages (which run on top of TCP) to establish a connection to the PPTP server and negotiate a set of tunnel addresses. The PPP process at the PPTP server assigns both a local and a remote address for the resulting PPP tunnel. After the user has authenticated successfully, a Generic Routing Encapsulation (GRE) session is built from end to end that sustains the PPP connection just negotiated. Only after these steps have taken place can both peers start exchanging IP packets. Note that the addresses of the PPP-encapsulated IP packets are negotiated by the two endpoints and do not have to be legal Internet addresses.
NOTE While the PPTP specification is solid overall, Microsoft's implementation has come under scrutiny over the last few years. Some improvements have been made, but I recommend that you take a quick look at http://www.counterpane. com/pptp-faq.htm1 for more information on this controversy.
While Microsoft bundles both a client and a server implementation in its Windows platforms, there is an open-source PPTP server for Linux that can interoperate with the Windows-supplied clients. This implementation, called PopTop, is discussed in the next section.
Continue reading here: Kerberos
Was this article helpful?