Recover Lost Files And Folders
Card Recovery Professional

More Information
CardRecovery Pro is software designed to help users retrieve their files. When an individual loses or deletes a photo, video, document, audio among others accidentally or knowingly, he or she can sue the software to get them back once again. Additionally, the whole process of recovery is safe, secure, and fast. Plus, if you cannot recover the files, you can contact their support team to give you a way forward. The good thing is that you will get a quick response. Moreover, there are several features of this software that can be enjoyed by a user. Nonetheless, some of the devices supported with the CardRecovery Pro include SD cards, MMC cards, Memory sticks, SmartMedia, USB flash drive, and so on. To get started, you can buy the software and download it on your device to stay safe. Therefore, with this system, you can retrieve your lost photos, documents, audio files, videos, and so on. Remember, the process is simple and fast. Read more...
Card Recovery Professional Summary
Contents: Software
Creator: LionSea Software Co., Ltd
Price: $39.97
Access Now
My Card Recovery Professional Review

Some users might complain that the default interface is more complicated than it needs to be. If you just panicked grab a quick drink and relax because this baby has a full customizable interface.
However, Card Recovery Professional is a fairly good program considering the standard and depth of the material it provides. In addition to being effective and its great ease of use, this software makes worth every penny of its price.
Linux Command Quick Reference
Deletes the specified files or (when the -r option is specified) recursively deletes all subdirectories of the specified files and directories. The -i option causes the command to prompt for confirmation the -f option suppresses confirmation. Because deleted files cannot generally be recovered, the -f option should be used only with extreme care, particularly when used by the root user. CHKDSK
Analyzing and Repairing Ext2Ext3
If you happen to encounter problems on your Ext2 Ext3 file system, the file system offers some commands that can help you to analyze and repair the file system, as described in this section. This information may also help when recovering deleted files. Imagine that a user tells you that he has created three files, home user filel, home user file2, and home user file3, but has accidentally deleted file2 and desperately needs to get it back. The first thing you can do is use the lsdel command from the debugfs interface. Chances are it will give you a list of deleted inodes, including their original size and deletion time. Listing 5-7 shows an example.
Undeleting Files Using mc
The Midnight Commander can make use of a virtual file system and includes a special undelete file system that can be used on ext2 3 partitions. The mc utility is just an interface to the ext2fs library, and the virtual file system handles for you the nitty-gritty details of the file system that the previous paragraph alluded to. As with any simplified solution to complex issues, mc must make some assumptions for you that might result in less data being recovered than if you use the manual method. For that reason, using mc for recovering deleted files is not a standard method. Be patient because it will take quite a while for the deleted files to be displayed. You will see a list of inodes that you can examine with the text editor (using the F4 key) then use the F12 key to perform a Save As operation, renaming the file to something appropriate for your use. Repeat this process until you have renamed and saved all the files. Press the Shift+F10 key to exit when done.
Copying Files Using mc
The Midnight Commander (available in the Universe repository, under the package mc see Chapter 7, Managing Software for how to enable the Universe and Multiverse repositories) is a command-line file manager that is useful for copying, moving, and archiving files and directories. The Midnight Commander has a look and feel similar to the Norton Commander of DOS fame. By executing mc at a shell prompt, a dual-pane view of the files is displayed. It contains drop-down menu choices and function keys to manipulate files. It also uses its own virtual file system, enabling it to mount FTP directories and display the contents of tar files, gzipped tar files (.tar.gz or .tgz), bzip files, DEB files, and RPM files, as well as extract individual files from them. As if that was not enough, mc contains a File Undelete virtual file system for ext2 3 partitions. By using cd to change directories to an FTP server's URL, you can transfer files using the FTP protocol.
Objective 5 Maintain an Effective Data Backup Strategy
Regardless of how careful we are or how robust our hardware might be, it is highly likely that sometimes data will be lost. Though fatal system problems are rare, accidentally deleted files or mistakes using mv or cp are common. Routine system backup is essential to avoid losing precious data.
Quickly create graphical text banners
Ubuntu's shred can help in both situations. It simply overwrites a file (or hard disk removable storage) over and over again with random data, so that the original data isn't recoverable (even by extremely specialized data recovery agencies, or so it's claimed by shred's creators).
Deleting Files and Directories
But how do you get rid of files Again, this is relatively easy, but first a word of caution the shell doesn't operate any kind of Recycle Bin. Once a file is deleted, it's gone forever. (There are utilities you can use to recover files, but these are specialized tools and aren't to be relied on for day-to-day use.)
Types of Incremental Backup
Warning Incremental and differential backups store new files, but most backup programs don't record the fact that deleted files have been deleted. Therefore, a full restore from a complete set of backups may include more files than were stored on the system at any given point in time. (A very new backup program, Duplicity, http www.nongnu.org duplicity , claims to record information on deleted files.) If disk space is tight, or if your users regularly create and delete very large files, be sure to consider this fact when designing a backup plan, lest you run out of disk space when you restore data.
Using Text Based Email Clients
Search forward for text using slash ( ) or backwards using Escape slash (Esc- ). Type n to search again. Press Tab to jump to the next new or unread message. Or go to the previous one using Esc-Tab. Type s to save the current message to a file. Type d to delete a message and u to undelete it.
NFS Kernel and Package Options
NFS has undergone several revisions over the years. These NFS version numbers are often appended to the NFS acronym, as in NFSv2 for NFS version 2. This level is the default in the Linux kernel options to use NFSv3 or NFSv4, you must activate extra features, which are visible in Figure 24.1's menu. As of the late 2.4.x and 2.5.x kernels, NFS support through NFSv3 is reasonably stable and complete. NFSv4 support is still considered experimental as of the 2.5.66 kernel (the latest as I write). I recommend avoiding the use of an experimental NFS driver it may result in poor performance, lost files, or other problems.
Recovering individual files
As an example, let us pretend that the user joe has accidentally deleted his Mail subdirectory from his home directory. Joe happens to be your boss, so it is urgent that you recover his files. Here is how you may go about it. As an example, let us pretend that the user joe has accidentally deleted his Mail subdirectory from his home directory. Joe happens to be your boss, so it is urgent that you recover his files. Here is how you may go about it.
Supplying an initial bashrc file
This sample .bashrc file creates aliases for the rm, cp, and mv commands that result in the -i option always being used (unless overridden with the -f option). This protects against the accidental deletion of files. Next, the file executes the etc bashrc (if it exists) to read any further global bash values. This file also sets the search path.
Begin the DrakX Installation
Before jumping into Mandriva, you need to check the status of your coexisting Windows installation. Select the Windows entry from the Linux boot loader and launch Windows. Windows NT, 2000, XP, and 2003 Server should launch CHKDSK to examine the integrity of the partition and then reboot.
Supplying initial bashrc and bashprofile files
This sample .bashrc executes etc bashrc (if it exists) to read any further global bash values. Next, the file creates aliases for the rm, cp, and mv commands that result in a -i option always being used (unless overridden with the -f option). This protects against the accidental deletion of files.
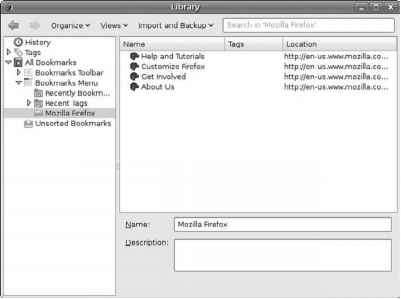
Managing Your Bookmarks
I tend to save my bookmarks in HTML every week or two, giving them names containing the current date, like bookmarks-27-0ct-06.html, so that I can tell one from the other. This makes it easy to find a specific bookmark in one of these files if you've accidentally deleted the bookmark but have some idea of the last time that you saw it. JSON is a fine format, but it isn't supported in other browsers or in older versions of Firefox, and I also like to put a copy of recent bookmarks on my Web site to help me find my favorite bookmarked locations even when I'm not in front of my primary machine.
Before you begin
Initially, Linux used the minix file system. This had restrictions and performance problems, which were solved in April 1992 by the Extended File System (ext). The ext file system was developed as an expandable and powerful file system for Linux. In January 1993, the Second Extended File System (ext2) was released. It has become the most successful file system for Linux and is the standard file system for most Linux distributions. While being a very solid, stable file system with good performance, it is quite slow to run a file system check (similar to CHKDSK). This occurs when the system fails and is being brought back up or every twentieth time the file system is mounted. On a system with big partitions, this check can take a while and the system is inaccessible during the check.
Using ReiserFS
Reiserfsck The reiserfsck tool checks the consistency of a ReiserFS file system. It has some powerful repair options. One of them is --rebuild-sb, which stands for rebuild superblock. Use this option when you get the error Read super_block can't find a ReiserFS file system. Another option is the --rebuild-tree option, which I hope you will not see too frequently. This option is required when reiserfsck isn't able to repair the file system automatically because it found some serious tree inconsistencies. Basically, the - -rebuild-tree option will rebuild the complete B-tree database. Before using this option, always make a backup of the complete partition on which you are running it, and never interrupt the command, because it will definitely leave you with a file system that is inaccessible.
The Trash Bin Folder
The particular benefit of a Trash bin on a UNIX-based system is that deleting files is permanent. No Undelete feature is included as part of standard Linux or UNIX. The Trash bin lets you move unwanted files out of your way, but save them for a while in case you need to retrieve them.
The Trash
To restore or undelete a file, click the Trash icon and a window will open up displaying its contents (see Figure 4-26). You can then drag and drop the files shown to other places in the computer's filesystem, or right-click any item for a list of further features, including options to permanently delete or restore a file. There is also an Empty Trash button in this window.
Cleaning Up
The rm command, especially with the -rf parameter, is very dangerous. It recursively removes an entire directory without stopping to verify any of the files. Run as the root user, this has the potential to really cause problems on your system. Be very careful and make sure you are erasing what you mean to erase. There is no undelete command.
File Recovery Tools
Undelete utilities for Linux are few and far between. The Linux philosophy is that users shouldn't delete files they really don't want to delete, and if they do, they should be restored from backups. Nonetheless, in a pinch there are some tricks you can use to try to recover accidentally deleted files. One of these tricks is the recover utility, which is headquartered at and available with most Linux distributions. Unfortunately, this tool has several drawbacks. The first is that it was designed for ext2fs, and so it doesn't work with most journaling filesystems. (It may work with ext3fs, though.) Another problem is that recover takes a long time to do anything, even on small partitions. I frequently see network programs such as web browsers and mail clients crash when recover runs.
Kyle Rankin
Everything you might have been told about the rm command isn't entirely true, and by the end of this article, you'll find that Linux does have an undelete of sorts. there is no way you can get it back. Undelete commands were for DOS users anyway we Linux users knew better, right Well, it turns out, we don't. Most Linux users I know have deleted the wrong files at least once in their lives. Now, the best protection against this is a backup (noticing a common thread in this series ), but if you don't have a backup, you aren't completely without hope. Everything you might have been told about the rm command isn't entirely true, and by the end of this article, you'll find that Linux does have an undelete of sorts. It turns out that accident-prone Linux users aren't the only ones who want to recover deleted files. In fact, deleted file recovery is particularly useful for forensics, as attackers might try to delete files to cover their tracks.
Using LILO to Boot
Linux manages the hard disk and user spaces in RAM, using i-node tables to maintain the disk information and a memory manager for user information. Linux writes any changes to the i-node tables to the disk drive every so often, but it maintains the RAM copies as the most recent because of RAM's greater speed. If you shut down the power before Linux writes any changes to the disk, the disk contents and the i-node tables written on the disk may not match, causing lost files and an incorrect list of what disk space is available. Even worse, if Linux was in the process of writing the i-node table or any other information at the moment the power is turned off, the write process is interrupted, and disk head crashes or bad sector information can result. The same principle applies to any processes that are running. If, for example, you were running a database reindex when you killed the power, the indexes and databases may be corrupted.
File Attributes
There are easily imagined practical situations in which you might want to use this functionality to prevent accidental deletion. For example, you might want to set this attribute on certain configuration files so as to force yourself to think very hard before modifying them. Use of the immutable attribute on particular system files is also often recommended as a way of adding an additional level of security to the system.
Linux Commands
The fsck command checks the integrity of a file system and carries out any necessary repairs. Depending on the type of file system, fsck runs an appropriate command to check and repair the file system. For example, to check an ext2 file system, fsck runs the e2fsck program. You have to run fsck when you power down your system without running the shutdown command. Typically, fsck is automatically run during system startup.
Journaling
Keeping a journal entails more work for a file system than a nonjournal method. Though all journaling systems maintain a file system's directory structure (what is known as the metadata), they offer various levels of file data recovery. Maintaining file data recovery information can be time-consuming, slowing down the file system's response time. At the same time, journaling systems make more efficient use of the file system, providing a faster response time than the nonjournal ext2 file system.
More Products
| WiseRecovery Data Recovery Software |