A VPN Primer
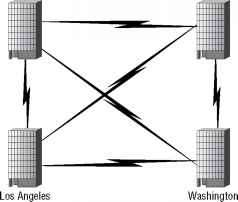
Consider a company named ACME Enterprises that has four separate geographical locations: Sales in Boston, Engineering in Washington, Human Resources in Denver, and Marketing in Los Angeles. In the traditional wide area network (WAN) model, ACME's IT organization would have to lease, maintain, and support six dedicated WAN links to have a full mesh network, with the associated distance-sensitive telephone company charges in order to ensure full connectivity among all four of its branches. (Figure 12.1 illustrates this situation.) Chances are that at least two of these locations (Sales and Marketing) are going to need access to the Internet, so ACME's IT department will also have to lease two dedicated circuits to the nearest ISP hub.
Figure 12.1 ACME's WAN connections
Denver Boston
Denver Boston
This setup is less than ideal. The Boston (Sales) and Los Angeles (Marketing) branches have two separate leased lines for private data and Internet access. And that is only the beginning. The real inefficiency of this approach is in evidence whenever ACME decides to branch out to a new location. Let's say that an ACME manufacturing facility is opened in Seattle. The IT department must now purchase dedicated lines from Seattle to all four existing branches. Furthermore, the more branches that ACME opens up, the more prohibitive it becomes to connect them to the existing locations via dedicated leased lines.
Virtual private networking capitalizes on the ubiquity of the Internet to offer a cost-effective, distance-insensitive alternative to private WAN links. There are two steps to building a VPN:
■ Connect all branches to the Internet by purchasing a connection to an ISP with a local point of presence (POP), also known as a hub.
■ Once all branches can reach each other via the Internet, build virtual links over the existing Internet IP infrastructure to ensure the confidentiality and integrity of the data as it travels from branch to branch.
Figure 12.2 shows the ACME WAN network using a VPN design.
Figure 12.2 ACME's VPN connections
ISP hub
Denver
ISP hub
ISP Backbone
ISP Backbone

- ISP hub
Los Angeles
Washington
Washington
The advantages of VPNs over dedicated leased lines are three-fold:
Distance-Independent Connection Costs The fact that each new corporate branch can connect to the other branches using an Internet connection, regardless of the location of the rest of the branches, reduces cost. The cost of the local loop is kept to a minimum and is often bundled into the monthly charges from the ISP. In addition, some ISPs offer discounts with quantity connection orders and now all of the offices have Internet access also, but this would not be a benefit in some cases.
Topology-Independent Connection Costs Corporate WANs come in three flavors:
■ hub-and-spoke, where all branches connect only to a central office
■ fully meshed, where all branches are fully interconnected to one another.
■ partially meshed, where branches are connected to one another according to business needs.
The fully meshed topology realizes the highest savings when deployed using VPN technology. Since each new branch is simply being connected to the Internet, the cost to incorporate the second branch is the same as connecting the 20th branch or the 200th branch.
Reuse of Existing Internet Connections Connections to the Internet are now as necessary to conduct business as fax machines and package delivery. VPN technology allows your enterprise to use a single circuit for both private corporate communications and general Internet access, provided that you have configured the separation of both traffic types properly (more on that later in this chapter).
WARNING Regardless of whether you'll be using your ISP circuit for VPN-only connectivity, or for VPN+Internet connectivity, you should protect your network perimeter by installing a firewall device. Chapters 9, 10, and 11 show you how to design, deploy and maintain a firewall at the network, transport, and application layers respectively.
At the heart of VPN technology is the ability to encapsulate VPN traffic inside normal IP traffic in order to protect the private data as it travels through the public Internet. Two separate security protocols have emerged as alternatives for the encapsulation and protection of VPN data:
■ Microsoft Corporation's Point-to-Point Tunneling Protocol (PPTP)
The following two sections are devoted to the discussion of these two specifications.
Continue reading here: IP Encapsulating Security Payload ESP
Was this article helpful?