Linux Security
The Samba Server
Samba is a full-featured implementation of a Server Message Block (SMB) server, which can offer transparent file services to Windows (95, 98, NT, 2000) clients, as well as to OS 2 clients. The brain child of LinuxCare's Andrew Tridgell back in 1992, Samba is now widely used and updated with help from programmers from all over the world. Samba allows network administrators to use a Linux server's ability to store and manage a large number of files, while still preserving the use of Windows-based...
Configuring the Secure IMAP Server
The imapd-2000 package uses OpenSSL for its secure transport options (imaps). In order to configure the SSL service, simply create a self-signed certificate using the following commands This results in the creation of the file usr share ssl certs imapd.pem, which contains both the key and the certificate that imap-2000 will use to add SSL protection to the IMAP exchanges. Note that IMAP inserts two files in the etc xinetd.d directory, as shown in the steps in Listing 6.7. ramon cd etc xinetd.d...
FWTK The TIS Firewall Toolkit
The Firewall ToolKit (FWTK) is a complete application layer firewall package freely available on the Internet. FTWK can be compiled to run on a Linux server without any source code modifications. First released to the public back in 1993, FWTK was written by Trusted Information Systems (TIS), now part of Network Associates International, with funding from the U.S. government through the Advanced Research Projects Agency (ARPA). Marcus Ranum, who is now a legendary figure in Internet security,...
Installing SOCKS5 with RPM
Use the rpm command with the -q (or --query) option to see if SOCKS5 is already installed on your system If SOCKS5 is already installed, but you would like to upgrade the installed package to a more recent version, use the -U (or - -upgrade) with the new version of the package ramon sudo rpm -U socks5-1.0r11-1.i386.rpm ramon rpm -q socks5 In addition to the base server package (SOCKS5), I recommend that you also install three additional RPM packages The SOCKS5 Linux clients (socks5-c1ients) The...
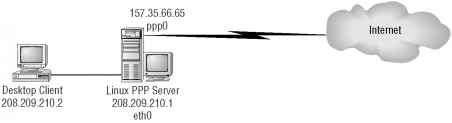
Sample Firewall Scenarios
The following example scenarios should capture the most popular network architectures in place today, from the simple dial-on-demand connection to a complex scenario featuring a dedicated router and a demilitarized zone where you can offer public services without compromising the security of your private network. Most small enterprises or branch offices have a single, non-dedicated connection to the Internet, and they don't want anyone coming back into their network or their firewall....
Managing Kerberos Credentials
The non-privileged user interacts with the Kerberos system to manage the Kerberos tickets that are used to request network services. There are four commands used for this purpose klist The klist command displays a list of the Kerberos tickets that you are currently holding. The ticket information is kept in the file tmp krb5cc_XXX, where XXX is your UID on the Linux server. kinit The kinit command requests a ticket-granting ticket from the KDC and holds it in the tmp krb5cc_XXX file for...
Disabling rhosts authentication
Although most current Linux distributions no longer come configured for this type of authentication, a few older systems may still be vulnerable. First and foremost, make sure that your inetd.conf file does not include support for the rlogin daemon. The command ramon grep rlogin etc inetd.conf should not return anything. If you do have rlogin enabled, simply delete (or comment out) the offending line and restart the inetd daemon. The r series of remote access commands (rsh, rlogin, rcp) are...
Network Based Auditing Tools
While there have always been attempts to build a comprehensive tool for exposing network vulnerabilities on a system, it wasn't accomplished until 1995, when Dan Farmer and Wietse Venema (who also created TCP Wrappers) released the first version of SATAN (Security Administrator's Tool for Analyzing Networks). This network-based auditing tool quickly became a household word among network and systems administrators. In their 1993 landmark paper, Improving the Security of Your Site by Breaking...
The runsocks Script
The SOCKS5 distribution comes with a compile option to build a dynamically linked library ( usr 1oca1 1ib 1ibsocks5_sh.so) that can be used by native Linux client applications in conjunction with a SOCKS5 server. The script usr local bin runsocks works by adding the location of the SOCKS5 dynamic library to the front of the standard Linux LD_LIBRARY_PATH, and effectively SOCKS-ifies any standard Linux network clients by replacing references to the commonly used Berkeley Sockets systems calls...
The Present Netfilter
Linux kernel 2.4 includes a number of features and stability enhancements that make it a very robust platform to use for your firewall. One of the most noticeable improvements of this kernel version is the packet-filtering subsystem, which is now named Netfilter. The development of Netfilter has been largely funded by Watchguard Technologies. This U.S.-based company develops and markets commercial firewalls appliances based on Linux platforms, as well as security services based on their...
System Monitoring and Auditing
M onitoring your system for abnormal behavior is an essential task in both system administration and information security. Most attackers leave their fingerprints in the system log files, and examining these logs is a fundamental step in the process of network forensics. More important, examining log files on a regular basis, looking for erratic or suspicious user behavior, can prevent attacks and enhance the overall security of your server. There are attackers who may be able to penetrate your...
Installing the FWTK Firewall Toolkit
Due to the special terms and conditions in the licensing agreement, FWTK is only available for download via FTP from the TIS FTP site. You have to read the license, agree to it, and register your identity on their site before actually downloading the software. Start this process by reading the text file located at ftp ftp.tislabs.com pub firewalls toolkit LICENSE. After you've reviewed this license agreement and found it acceptable, send an e-mail to the address fwtk-request tislabs.com that...
The Nec Socks5 Proxy Server
The NEC NSL SOCKS reference implementation was a pioneer in the field of application layer security, offering a full-featured proxy server application based on version 5 of the popular SOCKS protocol. This chapter walks you through the process of compiling, installing, and configuring the Linux version of NEC's SOCKS5 implementation. It also describes how to use SOCKSCap, which is a WinSock-based library that provides seamless SOCKS support for Microsoft Windows applications that are not...
The Legacy ipfwadm and ipchains
Starting with kernel version 1.2.1, Linux has offered a number of utilities to configure the rules used by the kernel to accept or discard IP packets. The first incarnation of this utility was Alan Cox and Jos Vos' ipfwadm utility, which was based on BSD's ipfw utility and worked with kernel versions 1.2 through 2.1. The last version of ipfwadm was released in July 1996. Starting with kernel version 2.1.102 and later, ipfwadm has been replaced by Paul Rusty Russell and Michael Neuling's...
Inetd Configuration Examples
By default, Linux distributions are shipped with a generous set of daemons in the inetd.conf file. Consider, for instance, the standard etc inetd.conf file that is shipped with the SuSE 7.0 distribution, as shown in Listing 4.2. (The comment lines in this etc inetd.conf file have been removed for simplicity.) Listing 4.2 A typical default etc inetd.conffile http-rman stream tcp nowait.10000 nobody usr sbin tcpd usr sbin http-rman swat stream tcp nowait.400 root usr sbin swat swat The system...
Pluggable Authentication Modules PAMs
With the explosion of network-aware Linux applications, authentication has become an important issue. Traditionally, Linux application developers included their own authentication mechanisms in their programs, ranging anywhere from no authentication (e.g., TFTP) to strong Kerberos and S Key authentication (e.g., telnet). Hard-coding authentication into each application has several drawbacks The user is forced into a specific mode of authentication. Changing authentication mechanisms involves...
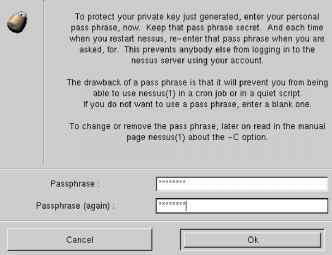
Configuring the Kerberos Domain Controller KDC
There are three distinct phases to configuring a Kerberos authentication environment < 1. First, you need to configure your Kerberos KDC, which listens for ticket requests from Kerberos clients. 2. Next, you have to populate the database on the KDC with the Kerberos principals for which you will be seeking authentication. 3. Finally, you have to configure your Kerberos-enabled servers to make use of Kerberos authentication for popular services such as Telnet and FTP. All Kerberos systems need...
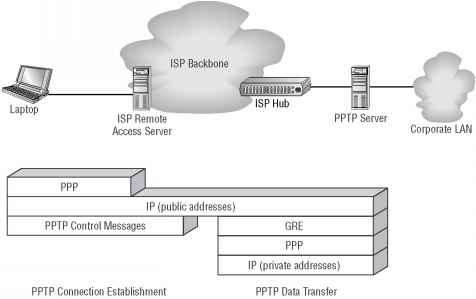
Pointto Point Tunneling Protocol PPTP
The fact that IPsec is a standards-based framework developed under the auspices of the IETF has made it the most widely implemented VPN technology to date. In addition, since IPsec is a mandatory element of a standards-compliant IPv6 implementation, its popularity is only going to increase as the new IP version starts to gain momentum. But there are other competing protocols in the field of virtual private networking that have enjoyed some support from the Linux community. One of those is PPTP....
SOCKS5 Shared Library Configuration
In order to control the execution of the SOCKS5 library and the operation of the SOCKS-ified clients, you must first create a configuration file, typically named etc libsocks5.conf. The contents of this file are analogous to the proxy-type directives in etc socks5.conf, discussed earlier in this chapter. The primary purpose of this file is to define which target hosts should be reached via the proxy and which target hosts should be addressed directly. Consider the following lines from a...
Configuring Windows SOCKS5 Clients
While it's fairly trivial to modify the Linux environment for SOCKS5 clients, there is typically also a strong need for Windows-based clients to use the proxy server to connect to the public Internet. You clearly cannot modify each Windows application to use the SOCKS5 libraries, so you need a shim, a network driver that will insert itself in the WinSock TCP IP stack and intercept all connection requests. The SOCKS5 developers augmented the capability of the Linux server with SOCKSCap, a...
A VPN Primer
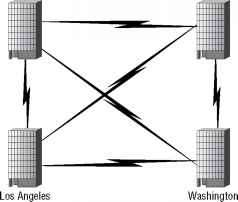
Consider a company named ACME Enterprises that has four separate geographical locations Sales in Boston, Engineering in Washington, Human Resources in Denver, and Marketing in Los Angeles. In the traditional wide area network (WAN) model, ACME's IT organization would have to lease, maintain, and support six dedicated WAN links to have a full mesh network, with the associated distance-sensitive telephone company charges in order to ensure full connectivity among all four of its branches. (Figure...
SMTP over TLS
Sendmail version 8.11 introduces support for secure SMTP over TLS (STARTTLS) per RFC2487. The term STARTTLS simply refers to the new SMTP command that is used to initiate the TLS-enabled mail transport session. This extension allows you to set up a secure bridge from two SMTP (Sendmail) servers that can communicate using TLS (also known as Secure Sockets Layer, or SSL). This ensures the privacy and integrity of the exchange and strongly authenticates the identity of the two communicating peers....
IP Encapsulating Security Payload ESP
While the AH solves the problem of IP packet integrity and authentication, it does not address the issue of confidentiality. In many cases, you need to make sure that nobody is gaining unauthorized access to the payload of your IP packets as they travel over an untrusted network. The IP Encapsulated Security Payload ESP specification allows for a security gateway to completely encapsulate a private outgoing packet before it travels via the public Internet. This can be done in one of two ways...
The pamcracklib Module
The pam_cracklib module provides strength checking of passwords before they are accepted. This module prompts the user for a password and checks its strength against a system dictionary and a set of rules for identifying potentially vulnerable password choices. By default, pam_cracklib prompts for a single password, checks its strength, and then, if it is considered strong, prompts for the password a second time to verify that it was typed correctly the first time. In addition to the checks to...
The netstat Command
The netstat command is one of the most powerful utilities available to you in your quest for a secure network configuration. While the process table shows you which daemons have been started from the command line, and the etc inetd.conf file shows you the ones that are inetd-controlled, the netstat command is the ultimate authority on diagnosing which ports your Linux server is listening on. The netstat command is very broad in function, but it is the --inet and -a options that show you the...
Spawning Internet Daemons with inetd
All Linux distributions (and all Berkeley-style Unix variants for that matter) include a central network service utility controlled by the inetd process. This super-server acts as the clearinghouse, or central point of administration, for all Internet services running on the server. You can verify that the master inetd process is running on your system by entering the following command root 421 0.0 0.0 1232 60 S Sep24 0 00 inetd The inetd daemon is started by Linux at system startup, and it...
SKey and OPIE
One of the major drawbacks of using conventional authentication is that if an attacker gains access to a password, they would be able to impersonate the user in question. But what if the password was different every time The concept of one-time passwords is what inspired Bellcore engineers to design the S Key system. By using a hash algorithm seeded by a small secret key e.g., a password , the S Key system allows you to use a predefined sequence of passwords to log onto a Linux server, using...